使用nginx,您可以允许和拒绝范围和ips( https://www.nginx.com/resources/admin-guide/restricting-access/ )。 使用realip模块,您可以在cloudflare之后将其使用的IP更改为真实IP。 ( http://nginx.org/en/docs/http/ngx_http_realip_module.html )
现在就是这样,我想将任何不是Cloudflare或localhost的ip列入黑名单。 这是相当困难的,我在设置real_ip模块设置之前尝试过它,而且没有雪茄。
这有可能吗? 如果用户没有通过cloudflare,这似乎是一个缺陷,它允许对某个虚拟主机进行更多的滥用。
有$ realip_remote_addr变量,但我不能在我的生活中找到一种方法来使用allow / deny而不是普通的$ remote_addr。
编辑:我注意到防火墙可以为此提供帮助。 不幸的是,我真的只需要几个vhosts。
Using nginx you can allow and deny ranges and ips (https://www.nginx.com/resources/admin-guide/restricting-access/). Using the realip module, you can change the ip it uses to the real IP after cloudflare. (http://nginx.org/en/docs/http/ngx_http_realip_module.html)
Now here's the thing, I want to blacklist any ip that isn't Cloudflare or localhost. This is proving rather difficult, I've tried putting it before setting the real_ip module setup, and no cigar.
Is this possible at all? It seems like a flaw if the user isn't going through cloudflare, it allows for a lot more abuse towards a certain vhost.
There is the $realip_remote_addr variable, but I can't for the life of me find a way to make the allow/deny use that instead of the normal $remote_addr.
Edit: It's been brought to my attention a firewall can assist in this. Unfortunately I really only need this for a few vhosts.
最满意答案
我认为你想要阻止你的机器的直接访问,即通过你的机器的IP。
您可以使用cloudflare设置的http标头。 每当通过cloudflare发出请求时,它会将$http_cf_connecting_ip设置$http_cf_connecting_ip访问您计算机的计算机的ip。
因此,您可以编写条件,拒绝所有具有空$http_cf_connecting_ip请求。
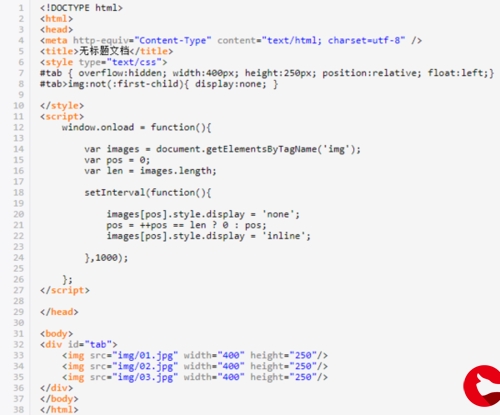
You can do it easily with a geo block
geo $realip_remote_addr $giveaccess { default 0; IPBLOCK1 1; IPBLOCK2 1; … } server { … location / { if ($giveaccess = 0){ return 403 "$realip_remote_addr"; #use it for debug } }更多推荐






发布评论